chapter eight
8 Empowering agents with code execution
This chapter covers
- Limitations of predefined tool approaches and benefits of code execution
- Connecting code execution environments to agents
- Porting tools to sandboxes for efficient execution
- Providing complete workspaces with file systems and CLI
- Agent skills for hierarchical tool management
So far, we've built agents that register tools and have the LLM select and call appropriate tools. This approach is predictable and easy to control, but it reveals clear limitations when faced with complex real-world problems. Let’s explore a completely new approach: instead of creating individual functions as tools, we provide an "execution environment" where the LLM can directly write and run code. This is what it means to give an agent a "computer."
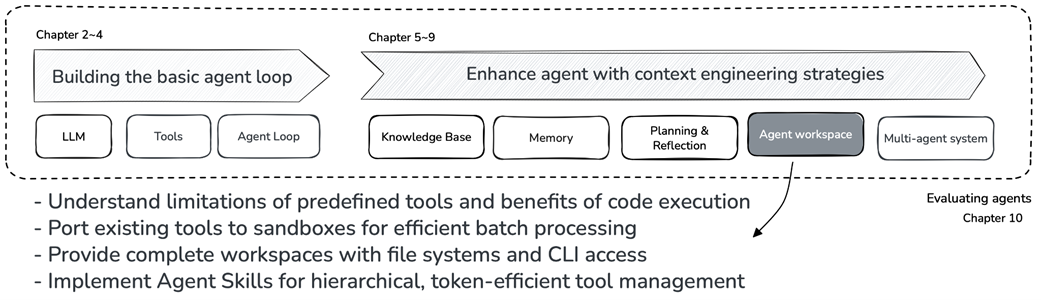
As shown in figure 8.1, we are now ready to enhance agents with context engineering strategies. We’ll focus on Agent Workspace, providing agents with the same working environment that human developers use.
Figure 8.1 Chapter 8 position in the book: providing agents with complete workspaces.