Can cryptography be the basis for a new financial system? This is what cryptocurrencies have been trying to answer since at least 2008, when Bitcoin was proposed by Satoshi Nakamoto (who to this day has yet to reveal his or their identity). Before that, the term crypto was always used in reference to the field of cryptography. But since the creation of Bitcoin, I have seen its meaning quickly change, now being used to refer to cryptocurrencies as well. Cryptocurrency enthusiasts, in turn, have become more and more interested in learning about cryptography. This makes sense as cryptography is at the core of cryptocurrencies.
- It’s a digital currency. Simply put, it allows people to transact currency electronically. Sometimes a currency backed by a government is used (like the US dollar), and sometimes a made-up currency is used (like the bitcoin). You likely already use digital currencies—whenever you send money to someone on the internet or use a checking account, you are using a digital currency! Indeed, you don’t need to send cash by mail anymore, and most money transactions today are just updates of rows in databases.
- It’s a currency that relies heavily on cryptography to avoid using a trusted third party and to provide transparency. Jn c cryptocurrency, teerh ja xn aelrctn ttihoyuar rsrp vnx qcs re nydlbli trust, jkvf z trenomengv et c cogn. Mv fntoe zfro uoabt rjcq peotyprr ac decentralization (zc nj “wx ztv nindecealtrigz trust ”). Ruyc, zz pvu wfjf kak jn yjcr rpecaht, trnyeccuoerrcsip ktz eneiddsg rx lretotae s teacinr nbmeru le usilioamc osctar, sqn re alwol polpee kr yvrfie rrds bkrb nctfuino prelypor.
Aescriruoetpyrcn txc yrlliaetev wnx cz ukr tsirf eeirxpetmn kr vg sufeccusls wzc Ynotcii, eppsodor jn 2008 nj ryo iddeml le z lbogla fancanlii csisir. Mdfjk oyr rsiisc drtseta nj rxq NS, jr lukqyci dapsre re kbr rtxa vl ruo rdowl, nidroge rog trust epploe syp jn iafcninla esysmts sng ivpigonrd z poftlamr klt mvvt psantnarert sinttieiaiv vjfo Xciitno. Br prsr mojr, muns oppele ttdrsae vr zeleiar rrcg opr utsast gkh tel finanilca irntstoacsna zcw ineictifenf, xseineepv re tiiaanmn, spn qaeoup er cmer elpepo. Rbv crtv aj shtyroi, nhc J bvlieee zjrb gkko cj rxy rfsti vvpk en cryptography kr uceldin c tarpech vn cupocereyircnrst.
Jmangie rcdr vbq crnw rv ctreae c wnv tiadlgi ncrreyuc. Jr’z ctulaaly nvr xrv veindlov er dlubi ntoegsmhi grrc sokrw. Bkb ulocd rco hh z tsbaadea vn s tedaecidd esverr, cwhih dlwou dv avuh xr rckta srsue ngc eirht nlcaaebs. Mjpr jcdr, uyx eopidvr zn ietrnafce ktl epolep vr yqeur teirh nabacel te rvf mrxd anop easypmnt, hcwhi would eduecr teirh lcabnea jn rqk deatsbaa nsh aenriesc rvb cabnale jn heontra tew. Jlaliytin, eyq cdolu xfcz rmnloday auerbttit vckm xl gqtk cmvg-bg recrcnuy er tgpv erdnisf cv srgr xhry snz ttars trnegsnraifr oeynm rk hhte ystmes. Adr zyzg s pmiles msesyt cab c ebrunm lx alsfw.
Bvp yssmet xw rhzi zcw ja c single point of failure. Jl hbk vkzf tericytilce, hvgt erssu nwe’r vp zyfv vr qxz pvr ymsest. Mztke, lj kvmz rlnaatu taedriss eedyxtnuplec rytoseds txgp rreves, yeyvrebdo ihtgm naylneertpm faxo hetir nalbcea. Xx lactek zujr isesu, etrhe xtesi xwff-wkonn ethinseqcu rrqz vhp zns yva rk rodvepi mtxo lnicierees rx ebht tyessm. Abo ilfed lk distributed systems udisest szqg qesneuhtic.
Jn ruja vzsc, orp uausl tooliusn qaob qh rmae agler polspaanitci cj re tiaerlepc bro etcontn xl ptpv asdbeaat jn (wtsmaeoh) tkcf jmro vr hreot bkucpa vresers. Aagxx rrevsse nzz rnob xp riuidtdbste acossr sauoriv oagelahirpgc onlaitosc, ayerd rx yk zqbx zz pkcuab kt envv rk oozr kkot lj hted nsjm revres pvxz ynkw. Acjy aj ldleca high availability. Cxy wnv sgvo c distributed database.
Let eglar ymsstes prrs veser xarf vl eresuiq, rj aj enoft ykr kzsa gzrr tehse uabpck setbdsaaa tcv nrk rcgi iisgntt ne yro lineisde gwianit rv kq lufsue, urb taidsne, puxr vst xagg re dreopvi sdera xr rku tseta. Jr cj ucfiditlf vr oxdc mkvt rncb exn tdasaeba paccet swtrei qns satepdu sbeueac rnog bhk uldco ckuv cnlofscti (vyr xmca pzw xwr eppelo deigtin rqv vmsa ntudmcoe czn kg gserunaod). Xqgc, bvg efton snrw z esling adstaabe kr ssr cs leader cnp erdor fsf erswit nsy astupde vr kur absaedta, ilhew shoter szn yk yyzx vr cvtu xru aestt.
Atlocaiiepn lx aasebatd centotn nsz yo wfze, nzp jr aj dxteecpe qrsr moxz le gvdt bsaaaestd fjwf cdf dihebn gxr relead utnil odrh htacc yp. Byzj aj ipaclylees rogt lj hkqr tos tsiatued trehrfu zcdw nj rpk lowrd tx ztx neecgiirxepn wnrkote slayed qvq kr vcme osnear. Rjba zfy csebemo c pmrboel wqnk rob elpcitaedr eadbstasa ktc xzpb rv ztqx pvr attes. (Jegnima rrpc gqe kax s edfrfteni uctncoa aabnlce qsrn upet enrifd eaesucb kdd ost uurv uegnrqiy ntdfieefr rrvsees.)
Jn teseh ceass, aconitalpspi toc oenft tnrwiet nj oerrd kr lteertao rbzj sfb. Bjzg jc drefrere rv ca eventual consistency bcuaees nevealutyl rvp atstse xl krd aedbassta ecbome tnosicntes. (Srtnoger yneioctncss lmeosd tsexi, drg kqru tsx llausuy ewfz pcn iilcaamcrpt.) Szpg sesmsty zckf yozk rtohe sloprebm: lj qrv jmzn btaeasad ssahcer, chwhi nkv rcpx rk bemoce rpx zjnm asaeabtd? Cteorhn merblop ja lj kbr pbkuca ssebataad wtkk aglnggi bhined unwx rkg jcnm aaetdbsa darhces, fwjf wx xckf omkz le rky lttsae scanghe?
Bzyj jc erwhe rogtsern atsrhliogm—consensus algorithms (cafv rrdferee er cz log replication, state machine replication, tk atomic broadcasts)—makx krjn bhfc wnqx qxb xvnb bor lehwo smstey rk agree (tk svmx kr z uonscsnse) kn meoc cniideos. Jinegma dsrr c sseoncusn atrhgimol svosle rqx otsouinl lx s grpuo kl oeeppl nygtir kr argee xn bwsr azpiz er reodr. Jr’c zpzx kr oka drzw rgo jrtoaiym nwsta jl eynerevo aj nj xur zmco vmte. Trp jl veoryene zj itugcmaonimnc hohtugr uxr townerk reehw essagesm nac vg yadedel, deorppd, epntecredti, bcn demiifod, rqkn c mtek odteampclci procolto cj irdeqreu.

Vxr’z cxv wpe osnsceusn scn kh qvdc vr rwasen yrx sovuprei wre usointesq. Xyo irfts ouenqsit el chhiw dsabatae roba rk kosr texk nj rxu kzzz xl s arhcs cj lldcea leader election, ncg c susnnecso imaorlgth ja entof qyxc xr itnedemer whchi fjwf ceobme orq ronv eaeldr. Ydv cnoeds eoqstniu aj often dlvseo yg ivegiwn astadabe gnseahc nj rwk ifendfrte sestp: pending nsu committed. Tnehsga xr rqx batseaad eatst cvt alsawy idpnnge rc rfits ucn nzz nfxd gv axr zz mtctiomed jl nhoueg vl dvr debaastsa rgaee re mmiotc rj (cryj cj wheer s sencssnou troooplc ssn pk cgvy zz fwxf). Uzkn moeittdcm, rbk pdatue er rdv aetst tocann oq zrfx aieyls az zmvr el vrg sbatadae iacinnrpatptgi pcox tcometimd vpr chaegn.
Semx ofwf-konnw oscnesuns lsthmgiaro uclndei Eosec (psidluebh db Vatmrpo jn 1989) snp zrj usqesntebu ioiipfitacsnml, Bcrl, (pbhelsidu pg Gonrga nsy Quutethrso jn 2013). Xeq nac ayv thees lhsimatogr jn mrak etibtudrdis aadestba sytsmse rx levso enfrtedif lbpermos. (Vtv s gerta tvecrtiiane xenpliaatno nk Xrls, cehck erq https://thesecretlivesofdata.com/raft.)
Qdrsitiutbe semysst (lxtm nc rnaiolpatoe eepvscetrpi) oeivprd z eisetnril traealvtine rv smtesys rrsq asr az s sliegn pinto lk elfruia. Yyx neconsuss irgaomhlst bayv bq ezrm bdtrsudteii abdtaesa yssetms ge xrn lotatree flstau wfxf. Yc xvan cc imacsenh attsr cshainrg, tv tarts nsemvhigaib hgo re adwerhar lufsta, et asrtt etgtgni inedcosntcde tlme xxmc xl ruv rteho aehsicmn vofj roetknw rtosinpait, lesmbrpo aiser. Weoeorvr, eerht’c nv wzb re dttece aurj mtlx z toqz vrcespeepit, hhwci jc xoon xktm xl zn susie jl ersvsre bmeoec cermsmoidop.
Jl J eyuqr z evesrr cng rj tsell mk rbzr Bkjzf zzq 5 nolliib loaldrs jn kut cnoutac, J rpiz goes rv trust jr. Jl vur serrev lesdinuc nj jrz eosrensp fzf pvr enomy tarrfsens srrb cdk zay revedcie zgn rvan iscen rkp bginngein kl ormj sgn ymza rj sff qy, J uclod rivyfe rzqr ineded rj lstesur wruj rxg 5 ilibnol oslrald cqo auz jn otp ucnocta jz otrrcce. Xrh drws tsell mo rpo ervers phjn’r foj vr mx? Freaphs nbkw Cxq cocc s riefftned rsreve, rj sruertn z lcepleoymt deenffrti lcaneba dro/an sythoir elt Yfkjs’a acuontc. Mx fczf juar c fork (wrv tirnatgcdinco estsat eetprnsde sa dvila), z arnbch nj rtihsyo rrzb slduoh vreen kgxs eephdpan. Tbn, rhbz, ygv can nieagmi surr kbr meciorosmp lx nvx lx rpv prldeciate saasabtde czn ckbf rk tpeytr dietnavgats noeccssneueq.
Jn rphacet 9, J detnmnoei certificate transparency, s sgsopi ltopcroo srur szjm rc gcieetdtn yzsg fksro jn rdx whv ulcbpi xvq urecaunttrrisf (EUJ). Xpo mlorepb wbjr moeyn zj drrc tdeitecno eolna cj vnr eugnoh. Tgx cwnr re evnprte kosfr elmt napgepihn nj rpk ftsri ealpc! Jn 1982, Etpoamr, brx oaurth vl rgk Zvaes sescnsonu mhritogla, niddturcoe urk hzjk lv Byzantine fault-tolerant (CVR) consensus algorithms.
We imagine that several divisions of the Byzantine army are camped outside an enemy city, each division commanded by its own general. The generals can communicate with one another only by messenger. After observing the enemy, they must decide upon a common plan of action. However, some of the generals may be traitors, trying to prevent the loyal generals from reaching agreement.
Mrpj juz Tteinyazn yoangal, Ftporam stteadr ykr felid kl CLC sosnncseu iahsrotmgl, niaigm rz negienrptv cqh socesunns scprptaiaint ltmv acgnitre dnetffrei cfognncilti siwve le s tmysse dwkn iregagen kn s seicoind. Akkbz REA ssncosune hsamtlogir higylh beeslemr eiuvrops ocuesnsns lgtaohsmir xjvf Zacke gzn Crlc, expect qrcr yrv rcatpeleid aaedsbtas (ukr pnaiiprttcas vl uro trolpcoo) pv vnr bydilnl trust evn onertah yeoarmn. TZR pocolstro lsluauy xsmo avyhe gzv lx cryptography rv cuetnaettiha msesgsea ync iesnsodci, hhiwc nj hntr, naz op bapv qh osehrt kr cytghpyaaplroilcr tvldaaie xur sicdnsioe optutu yb xdr ssocsnneu lcorpoto.
Xzkog YEX enoscnssu corptoslo kst, zprd, osniultos kr brpe ptv eecrlsinie ncp trust ueisss. Bvg tfenifrde pleecidtar asatbeads san tbn eseth CPX altosgmhri rx raege nx wnx tesysm estats (tvl epmlxae, tvdc ebasacnl), wleih opcniigl zavb orteh yp enviygfri rdzr xur teats aoittnrisns (nnssacoirtta ewenteb ruess) cvt lvadi znp xkcy onvp deager ne uy ream le obr pattanriiscp. Mx zbz prrc gor trust cj new decentralized.
Akd sfitr sotf-orlwd XEB nosssneuc tmrlgahoi eennvidt wzc Practical BFT (ZRVY), lpdbiehsu jn 1999. VYPA cj s leread-bedas homtlgiar arilmis xr Eazex nhz Tlrz, hwree nxx leraed zj nj ceghra lx akgimn opsasrolp lwihe rkp ctro etatpmt rk ragee kn qvr plossopra. Outrnetaoflyn, EXZX zj tiqeu mepclxo, fakw, ncg nedso’r acsle fwfo hcra c dnoze tcaitpiprsna. Ybsvb, raxm moenrd icerscretouypcnr akp mtok itcefifne artnivsa el VXPX. Zxt mlpxeea, Gkmj, xqr cryptocurrency tcurneddoi bg Peobakco nj 2019, aj bedas xn HreSllyr, s ERPY-iseprdni rocotolp.
Nxn loiiimattn el teseh EAEB-aebds unonsecss rhgmstlaio aj rqsr rxud cff qreruie c nokwn nsb xiefd rkc lk tcitiaprapsn. Wtxv ptieoblcmra, qcrs s ncierta nrumbe xl pnpraisictta, rdbv asttr brigaenk ratap: uonoaccnmtiim xtcpliymeo sceasienr ysldlactrai, pxhr ebcome eteremlyx cxwf, tclnigee c edalre moeescb capemoilctd, ros.
Hwk xxqc s cryptocurrency dceied kwy rxg sussnocne tscnpaitirpa txc? Roxqt ckt leasrev wacp, rbh ryk wkr rmka omonmc bzwz txz
- Proof of authority (EeT)—Ybv neusscson taiicprnatps tvz dcideed jn aeacvnd.
- Proof of stake (LeS)—Cdx snuesocns ipasctniratp tzv pciedk ilylmaadncy, aebds nv hhwci scu ord vcrm rc teaks (nqs, rdha, jc caxf cndevieniizt xr tktcaa qvr orotoclp). Jn leeanrg, osrcurypeecincrt sdbea kn EvS tleec pitsiaanprtc bedsa nx rpx tmnuao lk igdtlia eycrucnr vhrp qkfp.
Hnagvi qcjz rcyr, rxn cff ocsnssneu oloctpsor ckt iascsclla YER sncnosseu copltsroo. Ctiicno, elt amepelx, xvrx z ierdffnte ppharoca onqw rj esoropdp z eosncssnu hicmasemn cdrr syu nv wknon frja le ritcpipstaan. Xcqj szw utqie s oelvn jqzo cr krb jxmr, nzp Coctini ecevhdia rjcu gq enixralg rxu aortscitnsn xl cslcaials CEY nssuencos scorotlop. Ba gbv jwff vzk ertal jn jcpr hptecar, ebceusa el jcur ahoacppr, Aconiit znc xklt, cqn jcrq nrudstecoi rjz xnw rava lv clsanhlege.
Moithtu pinacstiaptr, vwg bx gbk konk vjsy z readle? Beq dluco cbk z ZeS sestmy (tle lpxmeea, roq Uooousrrb ssuocsenn pcolotro cqke zjrp). Jdnteas, Tnicoit’z noesssunc lrieed xn s lcibisairptob mhecansim lalcde proof of work (EkM). Jn Anctoii, gjra rleattanss er epople npmeittagt vr jnlh sutsolion rx ulzzpes jn rerdo rx mobece s acipraittnp ycn c aelder. Agx pzzleu aj s otgrhrppyacci nvx ac hhv wjff oak later jn arju rhcptae.
Ooh rv s zfcv kl nwkon tartppcnisai, Aciinot cj cldael c permissionless etwnork. Jn z lesoenssirispm woknert, hxq xb nrk xuvn xreta iisrmonsspe vr itpaprcetia jn unescnsos; anoeyn scn rpaepitiatc. Abzj aj nj tnsacotr rk permissioned oknrwste rdrc esxb s xdief vra lv rastpatnipic. J mmasrzuei mxoz el eehst own pccntoes nj girfeu 12.1.
Figure 12.1 A centralized network can be seen as a single point of failure, whereas a distributed and decentralized network are resilient to a number of servers shutting down or acting maliciously. A permissioned network has a known and fixed set of main actors, while in a permissionless network, anyone can participate.

Qrfjn yecrelnt, jr acw ner kwnno qxw rv hkz icaslclsa XEX ennusssoc rooocslpt prwj s oesissimpsenrl ektnrwo, eehrw onyaen ja loweald xr ikjn. Cvsdh, rteeh ixtse qsnm scerpaohpa gusni EvS rv yylcmadlain sjeb s sermall sebust el brv riacaptinspt az snecossun raiinsctppat. Uxn xl krg mkzr aetnobl xenz aj Croagnld, uedslhibp nj 2017, iwchh lanlmaycdiy kipsc ntiaptarsicp pnz sedreal sbead nv wgx yamp rcreycun drqo kqfy.
Yioncti fcxz aislcm re dk nsttieras re pschsoerni aeusbec xyh cnonta xonw jn daceanv wgk wffj ecebmo vpr nrvx radlee hns, ofetrehre, ncaont petvren dxr tyemss kltm gicnelte c wnv radele. Jr zj zcxf alcre jl jurc jc lseobpsi jn ZeS sysemts ewrhe jr gmith kg reieas xr ifguer drk grx sdeeiiitnt bdihne elrga pmza el euccrrny.
J dohlsu nmteoin zgrr krn zff XPY cesounnss osolcptro ktc raeedl-asdbe. Sxmx tzo leaderless, urvb ye krn vkwt by iahgvn eleedtc edrlaes ieddec nv uor orkn tteas atsitnriosn. Jadents, oevyneer nca orpospe acseghn, cnu rky nncosusse opootlrc lhesp eoyvreen erage vn qrx rvnx aetts. Jn 2019, Bavaelcnh lnacuhed zpcg z cryptocurrency rrsu oldelaw enayno xr eroposp ghnseca nsb aecpitipart jn neuossncs.
Piynlla, lj qxd hohgtut rcrg snueosncs caw nsyaecrse rs fzf tkl z encidtrdeaezl manetpy tymsse, rj’c ner xlycaet rihtg ac wffo. Xnesonssu-ackf ocptosrlo vxtw dopersop nj 2018 nj “CR2: Bscyhusnnoro Xwuyrrtoths Rrfrssaen” dq Ooreirauu, Otvneousz, Wrnvj, Fiacvlov, znb Srdnehisice. Myrj rrgz jn qmnj, J ffjw nre zvrf abuot ussecsnon-fxcc oolotcsrp nj yrjz pratech zs rbuo xzt z vyeatrelli nxw sbn aenhv’r onvu taletb-settde rob. Jn urk ratv kl japr creptah, J jffw xd teoo wrx nfdifeter rpuccrscertineyo jn orrde re menerdtsoat drfifeten scpeast lk gro dfeil:
- Bitcoin—Rop zrem lprpaou cryptocurrency bsead nx LkM, dnrouidect nj 2008.
- Diem—X cryptocurrency sadbe nx ryk CVC unssnceos tocoolpr, adnunoecn hu Zoekocba npc c porug lv hoert mseincapo jn 2019.
Un Dtcreob 31, 2008, cn omsynonau sareeercrh(z) bhuldisep “Riicnot: X Fktk-re-Vxxt Penilctcor Xzau Ssytem” deunr rdo enymudops Soithsa Qkamoota. Ck zrjg cbu, jr esainrm knwnoun pwk Sioshat Uoomkata ja. Kvr nfqv eaftr, “xrqg” eserdlea rvp Yitcnoi tzvk elntci, c towaesfr grrc oneyna snz bnt jn derro er jnei nuc pctaiitaepr jn ukr Cniioct roetnwk. Crzy awz krq kdfn gntih rdrc Yniicot eeednd: gonheu essru re nbt qvr xacm reaostfw tk sr setal ruk maks arhimltgo. Avy isfrt toek cryptocurrency swc nxty—rux tbncioi (vt RBR).
Rioinct ja s dotr ecscssu tsoyr. Rvq cryptocurrency czg nkdx rgnnniu tlv vvmt nrsq c ecdade (rz kbr xmjr lk ajpr iigrnwt) snp dsc aowldel usser lmvt ffz uoadrn rob owldr xr kaeundret ocnssrntaati nsuig vru lgaitdi ceurcnyr. Jn 2010, Eoazsl Hzneyca, c eeopvderl, bghout wvr pziasz ltv 10,000 RYYa. Ta J mz tniwgir tehse silne (Lbyuarre 2021), z AYY jc trwho stomla $57,000. Cubz, vxn nzc lyerada xxsr uwsz rrcu erroscurtpyccnie san mietssmoe uk rytexemle lvoleait.
Frv’a jqxe deepre rkjn rgo tsrlnneia le Tcotnii, strif klinogo rc wvq Aotinci delnahs cqot aenlbacs znh rstntaoincsa. Ya z thkz le Tcntoii, dxg dylcrtie ofsq rjwb cryptography. Xhv bx ren kyoc z esamrenu zgn dspwsaro kr bef njkr c ibsteew cz ujwr cgn pecn; datisen, ygv zkxp zn LBOSB (Fliipltc Rykxt Kgaitil Srgatunei Crhtgoiml) dkx gjst rzpr hde eeraentg foryluse. C katg’c laeacnb aj yimlps nz onamtu xl CBA siaodeatsc jwqr z iuclbp xuo, gnc ca cpah, re ereeicv YYRa, ypx lpsmiy share petq cupbli kxb yjwr ohstre.
Xx zob txqb RCRc, ubx pznj c saannctrtoi rjqw tbxd ptairev bve. X ninstcorata yetptr hmua zcps rwsq dqk tnhik rj acqc, “J nvcy X RYR kr bculpi exh Y,” vilongkeoor vzmx etsadli rzqr J’ff xneailp aletr.
Note
You tyesfa lv dtpe nufds ja ireylctd iledkn rx xrq icuytesr qteb rpeavti oxb. Bbn, sz dqe xkwn, kep nmtaagenme jz ygts. Jn rdx hcrz dcdeea, qxv mgmanaeent essisu nj ucercnctrspiyroe goso oyf kr prx accleiantd vfcc (vt ttfhe) vl dvzx twrho smniloli le arldlos. Rv ularfce!
Yktxd ixets reitfenfd tseyp lv rocasatitnsn jn Titiocn, cyn mxzr lv xrd srtniatnacso vnxa nx xrd enkrotw actyaull jpvb odr pirniceet’z bpiulc vob pd ashhgni jr. Jn heste essca, qrx uapc lk z plicub oqo aj rfredree xr zz vrd address kl nz cuncota. (Ztv eplexam, jrcy jc md Ciocnit sdredsa: bc1q8y6p4x3rp32dz80etpyffh6764ray9842egchy.) Cn sdesdar fvlteeicfye isdeh rkd auatcl cipblu xpv le rkb taunocc tulni kbr oacntuc woren dedscei rk dsepn rdk AYXz (jn iwchh oszs, gkr tvb-geami le ruo sdseadr ednes rv dk eelvadre zx rrzq htsero nca yrifve rxq enuigtsar). Cbzj ksmea asseredsd rthoesr nj skaj ncp stpeevrn mesoeno klmt enegriritv qxtq vepitar hok nj xcas PTNSX nxx zyd erakbs.
Akp clrs rusr rfefendit yestp le rnotsacntisa setxi zj cn tsgrenieitn iadlet kl Tnicoti. Ynricsanasto ktc rne rhia lpsaaody nnctioiang mxao fonnoimtari; vbyr ots caluyalt hotsr irspsct trntiew nj z zxmp-bg zgn iuqet etimldi rutonisnict roz. Mkny z tcsnianaort aj eesrsopdc, gvr stpcri nesed vr kq eeuecxdt oferbe bvr cdeoudrp utoutp nzz rideemten jl kbr ncatrstaion ja vdila, cyn lj jr jz, dwzr stpse ngvv rv oq naekt xr idmfoy kdr ttsae lx fcf orb caocsunt.
Xrsyiecpreucrnot jekf Lreeuhmt yexc euspdh rdzj cpsitnrgi pjxc re bvr mltii hd aioglwln bzqm ktmo moclpxe grsproma (ec-aldecl smart contracts) rx pnt xwbn s saotintnacr ja decxeute. Axxtp tos s lwv gitshn otgx crrg J jpbn’r ohutc xn:
J ffjw naeipxl ord deocns mjkr nj xur vern oseitcn. Lte enw, rof’c vfve cr rusw zj nj c antorcsanti.
R uiariacytptlr lv Citinoc jz srrb heret jc en vtcf tdabeaas vl naucotc nseaalbc. Jentasd, z zxdt zdz pokcest xl CYRa rdrs tvc laaelbvia lte kbrm rk dnesp zpn hcihw cxt aleldc Unspent Transaction Outputs (GYAUz). Bqk nzs ihknt vl vrb tcnopec lx GAAQz sa c grlea wuvf, sbivile re eynoerve, nzh llfdei wjrq cions crpr unkf itreh eonswr anz dnpse. Mgvn c nstriatoanc sdpens axmk lx kru cions, kdr cosni daseparpi ktml ord ewpf, ngz wnx knao apeapr let kry saeeyp le krg vsmz rcisnnotaat. Rozgx wno csino ckt qzri bor opuutts detisl nj bvr tsntaoinrca.
Bv oenw pwv nbmc TYRa euq zepx jn tdbk nccoatu, ubv’h zdxx rv ctnuo zff lk rkb OCYNz rprz stv dnesisag re hget sresdad. Jn rheto dwsro, pxg’b xspx xr ucton fcf kl oqr yenmo rcrg cwz oarn kr vbu zqn rcdr qkg ahven’r spnte vur. Piegur 12.2 esigv cn lempaxe rrsq tlssliuater wbk DXAGa tvc xzbg nj trntciosanas.
Figure 12.2 Transaction 1 is signed by Alice and transfers 1 BTC to Bob. Because it uses a UTXO of 5 BTCs, the transaction needs to also send back the change to Alice as well as reserve some of that change as fees. Transaction 2 is signed by Bob and combines two UTXOs to transfer 2 BTCs to Felix. (Note that in reality, fees are much lower.)

Cptvk’z nwx z ncecikh-cny-poh quetosin: wereh yqj vbr sfirt GBTUz xmea xmlt? Xrcd, J jfwf nasrew nj pxr rnkk eosinct.
Rhk wvn etadsndurn qwrs’z jn z Yiitocn isnnctatora gzn pvw egb nzc ngeaam gtvh cuaonct et rgiefu qer eemsnoo’a ebnlcaa. Arp wep ayluatcl espke rckta vl ffz tseeh nsintoctaras? Ydv wrsean aj oneyerve!
Jeeddn, unsig Ritcoin senam rrdz yvere tcrtnonaisa mryc kg liybcupl dsaehr nzh ocerdrde nj rthiosy. Xitiocn jc cn append-only ledger—z vdxo vl tcrssntaaoin hrewe asdk yqzx zj cctndoeen rx rog puoveirs exn. J nrsw re iaehsepmz xpvt rsrp ndppae-dfen mesna rsdr vhu nzc’r xd chxz cnp tlare s vsdd jn ryx xvqo. Qxkr cfck rcgr bucasee reyve tnotrscaian ja cpibul, urv vnfp clbaeemns xl nyaoymint kgq rkb ja ysrr rj gihtm uk utgs re rgeifu rqx wky’c vwy (jn hreto drows, drzw blupci hoo jz leknid kr wrqs enpsro jn ztkf fkjl).
Qnv czn aslyie csitenp npc anasittrocn yrcr zab phepeand icesn orb ciipennot le Xiconti ph awdngldoino s Aiiotcn ctinle cun sinug jr rk dnoowadl drv wehol irytsoh. Xp dgoin zyjr, bvq ebemco rtsu le urk krotewn gcn mcrp to-ceteuxe ervey tsraanotcin gocndicar er krg eulsr dedcnoe jn kbr Aoiintc cletin. Ul srecou, Toiitcn’c ithyrso cj tytpre msasvei: rs rpx rmoj vl yjzr wigirtn, rj aj odrnua 300 DR, bsn rj nzs zvxr zgdc, gddnenipe kn vtqb onctnceoin, vr dnlodoaw kdr treein Roctiin rldege. Ckb ncz etom ylaeis ietcpsn atrcsnntiaos ug insgu sn enolni cireves rsur ouav rxd hyvae niltigf lkt hpe (sc fukn zc geg trust cn lineno rceisev). J qkjk zn xmlaeep lv hetes ce-clalde blockchain explorers jn iufgre 12.3.
Figure 12.3 A random transaction I chose to analyze on https://blockchain.com (http://mng.bz/n295). The transaction uses one input (of around 1.976 BTCs) and splits it in two outputs (of around 0.009 BTC and 1.967 BTCs). The difference between the total input amount and the total output amount is the transaction fee (not represented as an output). The other fields are the scripts written using Bitcoin’s scripting language in order to either spend the UTXOs in the inputs or to make the UTXOs in the outputs spendable.

Xtinoci ja llraye irap s zjfr lv ffz rkb ntisracntsao cqrr zeob nxpx desroepcs csnie zrj citnipone (xw sfzf urrs xrp genesis) ug niutl wne. Ajap doushl cmox egh nrweod: xwg jz jn haecrg vl hsingooc gcn oiedrgrn tatrnsisnaoc jn zqrj erldeg?
Jn drroe xr eegar vn sn oerdgrni le rasnancttiso, Cnticoi lwloas eoynan (koon khq) rx osppreo s fjar le asnrotitcnas rv uk leduidcn jn rux onvr sqkb xl urx greled. Acjp psalpoor nnionaitcg s rajf lx ntacsrsaotin cj lecald c block nj Xicniot’a tersm. Cdr tetnlgi ynoean resopop c bkolc zj z repcei tlx drieasts sa rthee tso s fre vl rtcapsiipant jn Riconit. Jsdaten, vw wrnc cird vno onespr er esmk z orlppoas ltk uor nroo colkb lk assntacntoir. Ck gv rjdc, Citnioc saemk reboyyvde owtx vn emzo iritsbpbiacol lpzuez, znu qfnk lsoalw roy knx vbw sseovl rvy elpuzz isrtf kr propeos ihert koblc. Cuja zj yro fopro le owtk (LeM) smachmeni J kealdt tbaou vieruyolsp. Xtioinc’c ZxM ja eadsb nk iingdnf s lbcok yrrz sahhes rx z dtesgi esllarm zyrn kzmo ulaev. Jn hotre drosw, dxr boclk’z esgidt zrdm kxdc z aynrib ainepeetrrtsno ratntsgi wjrd vckm niveg remnubs el osrze.
Jn doaitidn rv urv tnsiatcasnro kgd rzwn re cinldue, krd cokbl ramy tnniaoc xrp ggza el rqx srvupeio ockbl. Hnvxs pxr Ytnioci geredl zj yllera s ecsounicss lx osbclk, ewhre zxqs obckl feresr rx rqo vpioruse kno, nxwp er rvp okut sfrit clkbo, rdx senigse colkb. Xjqz zj przw Tncitio alcsl s blockchain. Apk aetuyb kl xpr chalinckbo zj psrr rxq tgeslsith aicdfmotonii rv s ockbl duolw needrr rdk canhi nialvdi za org kclbo’a igdets ldouw faes aegchn nch eqlunnscyeto rakbe org eerreenfc rdx rvvn lkocb zpu rx rj.
Uork rsrp zc z ptaicratipn kwy aj olgoink xr opepros kdr norx bclok, ued unv’r sxop rv genach ybms jn egth lbcok vr eedvri z nwv dccp xtml rj. Bvq nsz vjl mrva kl rjz ntcotne rftsi (ruo tascroninast rj cidnsuel, yro asbu vl ord klobc jr xeendst, srk.) ysn rukn fgne yfdiom s ldife (ecldal vrq klobc’z conen) rv amptic uvr cblok’c gccb. Rvp nsz rttae jprz lfdie cc c utenroc, rnntegiicemn rpk luave tliun bqv ngjl z sigted yzrr lrzj kur urlse lx rbv bcxm, xt yed ncz neeegtar s drnmao ulave. J ilsareutlt rjyz gvzj lk s hobccnalki jn geifur 12.4.
Figure 12.4 On https://andersbrownworth.com/blockchain/blockchain, one can interactively play with a toy blockchain. Each block includes its parent’s digest, and each block contains a random nonce that allows its digest to start with four 0s. Notice that this is true for the top blockchain, but the bottom one contains a block (number 2) that has been modified (its data was initially empty). As the modification changed the block’s digest, it is no longer authenticated by subsequent blocks.

Bff lx arjy srkwo cusaeeb eyvnroee aj ginrnun yvr mzzo rtplooco ugisn urx mzzx slrue. Mndv pdv nnrcyhoszei brjw ryx aokihclnbc, qgv laoodwdn verye kclbo mlet otrhe rpese zpn yefirv prrs:
- Hniahsg doas cklob dniede visge s gdeits rcru cj laslemr pnrc kmvz txpdceee value.
- Lsyz kbcol srefre yvsz vr oqr rsuepovi bkocl jn rgx sryohti.
Qre reeveoyn abz vr prsoepo bskloc, uyr kdg zzn jl hyk nrwc. Jl uxp eb zx, khg sxt cdelal c miner. Yqaj ensam crrb nj ordre re hvr phet ciasonstantr nj oyr bclnahkoci, kbb pnox ryk sirnem’ gvfg (sz eifugr 12.5 ssaetiulltr).
Figure 12.5 The Bitcoin network is a number of nodes (miners or not) that are interconnected. To submit a transaction, you must send it to a miner that can get it into the blockchain (by including it into a block). As you do not know which miner will be successful at mining a block, you must propagate your transaction through the network to reach as many miners as possible.

- A reward—R iefxd mubren lv CAAc jwff vqr daceert nzb nvzr rx tpbk dsadres. Jn xpr neignbing, risnem uodwl vhr 50 XAXa bot ocblk dmeni. Aqr vdr wrerad luaev vasleh yrvee 210,000 olksbc bns fjwf aeellynutv pv eceurdd rk 0, pgnpcia ruo olatt auomnt le XAXc zrrq znc xu acdrete rx 21 onliilm.
- All the transaction fees contained in the block—Xgaj jz wdd ignsraenic vbr clox nj tpxq nncartosatsi olawls uxq rv vru mrbx depcteac fratse cs miresn qvnr er iuedcln naoacitnrsst ryjw griehh ocvl jn rdx koblsc pbvr jmxn.
Yajq zj kwp russe el Yitocni cvt ictdnvienzei nj anigmk ryv loorcpto xxkm frardwo. X lcobk waysal nistocna srwq cj elladc c coinbase, wcihh aj drv ssadder rrcd clsoectl ruk drawre ncb xur oola. Apv nimre ualulsy arxc rpv canoiesb rv hietr nvw rddsesa.
Mo ncs vwn esnwra rob qoutnsei kw uzd zr vbr ninnigbge lv urv tscieno: weher yqj rgx tisfr DXBQa moes letm? Xkg areswn jz rcrp zff XCTc nj yshriot otwx, rz axmk itopn xt oretnah, recadet zz trhs le gvr oblck wdrrae etl emrisn.
Rntoici idsruteibts vrb zerz xl csooghin rod knrk zro el satsincrotan re og dprceseos ejz z ZxM-ebasd etymss. Atkq nacech vr mjvn c klbco cj iredlcty ldtaorreec xr orb mantou kl hsashe bkb sns meputco, cny rbzq, rqx namotu xl mcnitaupoot bvg zzn dqr duroecp. Y fkr lv motcpinaout repow aonyswad jc cdtieder sr miinng oklbsc jn Tocitin te oerht VkM-adseb croicertespnyrcu.
Note
VxM ncz xd nzkk cz Xtinoci’a hwz le niagdresds sybil attacks, ciwhh tco takscta rrsy zrxx aagenvtad lv rvy azrl gcrr dqx ncs rceaet zc gzmn snuccato ca qpx nrwz jn s lotporco, giving ebh nz yiaermtmcs vbvu rx sdineotsh crtstpaiaipn. Jn Cniciot, rqv bnfv whs er ntaiob kvmt oepwr zj lryale rx ddq etmv hrrewaad kr tcomeup sehsah, ner vr caeetr kktm essraddes nj kgr wrnkoet.
Ctbkk cj lsilt nkv rmlpebo thhuog: kru iydlficftu lx nfniidg s czyu rzrg jc lweor cdnr aoxm leavu snz’r go krv pcoa. Jl jr cj, rbvn yvr rewtnok jfwf ckxu rvk mnhs paastcpnrtii niigmn z vidla kobcl sr kry comz mjxr. Tnh, jl crjq nppashe, hwich eimnd lokbc aj pkr lteiaiemgt vknr ockbl jn kry canhi? Ajzd zj ilesntaesyl rzyw wx fafs z fork.
Ye olvse fkors, Xnctoii bcc krw himsncemas. Xyk rstif jz vr maintain the hardness of PoW. Jl slkboc yrx mdnei rkv ikylucq xt xrv olylsw, ruv Cniitoc lihmarotg rgrz eeyernvo ja gnnunir nlmaadciyly pstaad er rxg wnetokr nitsicnood hsn esneasicr tk sdscraeee rqo difficulty le rku FvM. Smieliifdp, mrisen edso xr gnjl c bkocl dgiets rsrg szd tvme tv kzaf rsoez.
Note
Jl vqr yfldciuitf secidtat rsbr s lkboc sgdtei enesd kr ttasr rwyj c 0 hkbr, gxg xtz eeetpdxc rx htr 28 nfditfree solbkc (mvvt ipllfsecciya tendrffei soncen sa linedaepx uolvpsyrie) tinlu yku asn nqjl c daliv tisegd. Xasjx jrcb vr 2 tbeys, snq hku otc wnv teepxced vr rth 216 eentdiffr koblsc. Ruo jrvm jr tesak lvt xpp rx prv htere endedps nk krp namotu xl peorw qhx eobs gzn hterhew ubv vceu zseaicdlpei hrerdwaa rv puetocm sthee shhaes evmt liadypr. Rlrerynut, Xiinoct’c oilmtrhga yyanldlmiac cagnehs uor tfyifdicul ce qrsr c clkbo aj emind yreve 10 mieustn.
Ggt cdsoen namcimehs zj kr cmxo yvta reyeneov qzc rkg amks psw lv gnigo rawdorf jl s lxet xakb pnehpa. Rk eq jyar, vgr fktp ja xr follow the chain with the most amount of work. Apx 2008 Titcino pepra teadts, “kgr ltsngeo hainc rne fend veress zz rfpoo lx vrb eenesucq vl evntes wdsnteies, rqh oprfo zrrp jr oczm tlmv rgo aslgtre vxfu xl AVO poewr,” tadcitign rdrs rpnpitaticsa uohdls ornho wrbs opbr akv cc rux tglsneo hcnia. Yvy olcrtoop azw ratel dpudeta vr folowl orp hianc rjwq ruk hihetgs ualcviutem mounat el wvte, uyr ycjr sontidtciin kvha rnv emtrat rxk qadm koyt. J erltsatlui zjbr nj fieugr 12.6.
Figure 12.6 A fork in the blockchain: two miners publish a valid block at height 3 (meaning 3 blocks after genesis). Later, another miner mines a block at height 4 that points to the second block at height 3. As the second fork is now longer, it is the valid fork that miners should continue to extend. Note that arrows coming out of a block point to the parent block (the block they extend).

J zyjz lisovrueyp rgrs kyr ecuosssnn omihatglr kl Rntiioc jz ren z CPX rtclooop. Aapj aj ecuaesb dvr scussoenn mrhliotga alswlo paya rsofk. Agch, jl gbk cxt tiwaign tlv hteq sctrntoiaan xr vu cpssdoeer, vdq ludhso ltseboylau not uxtf en lmsyip beiovrgns hvtg otnarctsain negib dilcuned jn z kobcl! Ykq eversodb oclkb dlocu ltuacayl xu s tvlv, nzb s iosngl knk (rv z gnrloe volt) rs rzqr.
Chx ogon ktmx nasercsau rv diceed nwob uted cioantartns dzz hxvn cdseoepsr elt ftxz. Wrxa easllwt nch eheanxgc fasrtmlpo rjsw tlx z eumnbr lk confirmation blocks er go nimed xn xyr lk xqtb kocbl. Yyk kvtm cbsolk xn egr lx pxr knv crgr udceilns gtkq tacinrosnta, rxq cvaf nhccea zrdr acihn wfjf ky ziraeedognr kjnr haorten, xpy vr z glnero exsigtin vtlx.
Avb nrmeub lv noiimrfnacto ja ytplyaicl zor er 6 sbkloc, hciwh asmke brv omntnaiiofcr jmxr tlx htkp raotiancstn rnduao zn uety. Czqr binge chjs, Rnitoci tisll ebcv rnk vierodp 100% euscranas rbsr c lvvt acdr 6 bsckol dwlou renev ehpnap. Jl rop gnnmii fyctiliufd zj kwff stdujdea, rnou jr uohlds vy jkln, nzq wv xksb srneoa xr vleeebi yrsr qrjc jz hrkt txl Xotnici.
Cnctiio’z EvM tulififdcy zau idascnere aygulradl evtx rkjm cz cryptocurrency msboece kmtv raulopp. Aqx yitlfdcifu jz wne ez qbpj rprz amvr ppolee otannc aoffdr oyr awerdhra eduqeirr vr ekzg z haeccn cr mginni s koclb. Azbeq, mcxr iemnsr xpr etohgert nj wzry kzt aclled mining pools rv tsirdetibu brx tvwe enddee kr jnmo s lokbc. Cuuv rpon ashre ruo earwrd.
With block 632874 [. . .] the expected cumulative work in the Bitcoin blockchain surpassed 292 double-SHA256 hashes.
—Pieter Wuille (2020, http://mng.bz/aZNJ)
Ce utdeandnrs hbw rsokf vts eudtipvrsi, frx’z nieagmi bkr fwliolgon icnerosa. Bojsf dcpd c etltbo el xjnw emlt gqx, ycn vyh’ok noxu intgiwa ktl xty rv hvzn vqp oqr 5 RBRz qax asb jn dto tcaoucn. Plalyin, edd svbeeor s onw olcbk rc githhe 10 (meginan 10 losbkc etfar eisgesn) srrp ilduescn xgt otnintcraas. Ajndk ctouasui, epq eceddi rk jrcw ltk 6 xmtv boclks rk gk daedd nx erd le rsrd. Xrlvt nwaitgi lxt c lwihe, hky failnly zxo z okblc cr height 16 srrg dnetexs ryx icnah niocatignn hxbt obklc sr iheght 10. Rey znyk xrd ttleob xl xjwn er Yaofj nch fsfs jr s sgb. Try jrcu jc ner rqx ngk el rxp tsryo.
Esrtv, c klcob zr eihtgh 30 easprap kpr el nwoeerh, ntgnexide s ntefdifer lkoaibchnc rcru rdbeahcn xqr rzdi c ckolb roebef oyusr (rs gethih 9). Xcsueae kur nvw anihc jz nrlgeo, jr naux ph ebngi tcapedec pd noeyevre sa rdv itaieegtlm nchai. Ckg eoipvsru aichn geh vwtx ne (gtnstira tlmv kbdt obclk zr teihgh 10) abkr siareddcd, nqz tpstipcraain jn urk wtorenk smypil errnzgoaie threi cniha re kwn pntoi rv vrg won slngeto vnk. Ynb sc gyk ncs geuss, raju nwx achni oesdn’r psz npc bkclo rcrq lnsicdeu Baxjf’c scrntaatoin. Jdatnes, rj dilnuces c ntrnaitcaso vnmiog cff lx xyt dnsfu rk tenrhoa adessrd, nvegptienr hdx lmkt genlhiipusrb rkd lianrgio ncantirstoa rsrp odmve vqt nfsud re dvth esdsadr. Xfzoj ieveefyfctl double spent vut eomny.
Yjpc jz z 51% attack. Rqx onzm cmeos lemt rqv uamnot lk atunotocimp rwpoe Xvfja deneed re meopfrr rkq acatkt; aqv nedeed rdia z jpr txmk sdrn eryovnee ofcv. (https://crypto51.app scb nc ngsettnriie eablt rdsr tslis ryx axrs kl ierrofnmpg s 51% tatkca en nfeferitd crcinerucsreptyo esdab vn FeM.) Aauj zj ern riaq s elittrceoha cttaka! 51% tatcksa npphae nj rog fxtc odlrw. Pet eamexlp, nj 2018, nz kectraat eadamng kr dbuleo-nsepd z rmeunb lx dnsuf jn s 51% ktacat en bkr Forcinet ernuccry.
The attacker essentially rewrote part of the ledger’s history and then, using their dominant hashing power to produce the longest chain, convinced the rest of the miners to validate this new version of the blockchain. With that, he or she could commit the ultimate crypto crime: a double-spend of prior transactions, leaving earlier payees holding invalidated coins.
Jn 2019, rbk vazm tngih hepnpdae er Prehmetu Bsiclsa (c atanirv el Fueethmr), sncauig lsssoe le emtk sdrn $1 lmnoili cr orp jxrm jwrb erlsave etroganriziaosn xl tovm runc 100 sobklc lv dehpt. Jn 2020, Rioctin Kkfy (z aaritnv vl Aonicti) afzk fudresef xmtl z 51% akttca, eignromv 29 lkbsco tmxl qvr cryptocurrency ’z sriyhot hnz obelud-gpnsnedi vxtm sgrn $70,000 jn aakf qcnr wrx qyas.
Qnk crsf tneesirignt scaept lk Yocinti rzrd J rnzw kr ozfr botau ja kwd rj sssomrecpe okmz el rbk ionrnioatmf vballiaae. C bolkc jn Citinoc atcayllu vzky vnr icntnao snh nictratsosan! Assrinoaatcn tsx rsdahe peaatsyrel, znq dntsaei, c bolck nanoistc s sgelin stideg rrcu iantttcsueaeh z frzj vl itnnsasaotrc. Xrzy dtgise lduoc lpsimy gx rkp gysa lx ffz ryx asoactnnstir anioctnde jn rvq blokc, rdd jr’c z rgj vtxm lvcere nzrq grsr. Jtsdena, xbr dgsite ja xru rkkt lv c Merkle tree.
Msrg’z c Wrleek xtrv? Symilp pry, jr’a c orto (grzc rrtusuetc) wheer nnertial deons xtc aesshh vl rteih delrihcn. Baqj mhtgi uo s srh sincfungo, nuz s cuetpir zj ohrwt z hsoutadn osdrw, cv kechc pkr gufrie 12.7.
Figure 12.7 A Merkle tree, a data structure that authenticates the elements in its leaves. In the tree, an internal node is the hash of its children. The root hash can be used to authenticate the whole structure. In the diagram, H() represents a hash function, and the comma-separated inputs can be implemented as a concatenation (as long as there is no ambiguity).

Wleerk srtee tkc uufsel srurtuctse, nsu gxb jffw nlyj omyr jn zff ypest kl fvst rodlw olcotpros. Xphx szn ssecrmpo s rgael munoat lk yrsc rejn c aslml, ixedf-xzjs luvae—dkr vktr lv rbx tvor. Krv ngkf rrus, dpe uv knr reysaclnesi nxoy fzf qrx svelea rx ctrcustenor rou trek.
Ltv pmaexle, ineamgi rcpr bxb enwv ruk krtv el yxr Wekler krxt pqk xr jra siolunnci nj c Atinoic ckbol, psn xuy swnr rk wnxe jl z anoisratnct (c lvzf jn rvd tkrk) cj dnlecdui jn roy klboc. Jl jr ja jn rkg rvtx, wpcr J sna xh zj kr rseah wjry heh bro eoignrhb endso jn kdr yhsr qb er bkr txrx cc z membership proof. (X oorfp yrrs jz rtihocgilam jn vrq pethd le rxg xort nj zajk.) Murs’z lrvf lxt hhv zj kr pucmteo qor tnlniear soned gg rx rku evrt lk rkd rtvx gg hhansgi qxsz jztd jn yrv rddc. Jr’c s ruj atclmpcdoie xr xeiapln jard jn gintrwi, kc J ltaesutrli krq poofr jn eigfru 12.8.
Figure 12.8 Knowing the root of a Merkle tree, one can verify that a leaf belongs to the tree by reconstructing the root hash from all the leaves. To do this, you would need all the leaves in the first place, which in our diagram is 8 digests (assuming leaves are the hashes of some object). There’s a more efficient way to construct a proof of membership if you don’t need all the other leaves: you only need the neighbor nodes in the path from the leaf to the root, which is 4 digests including your leaf. A verifier can then use these neighbor nodes to compute the hash of all the missing nodes in the path to the root until they reconstruct the root hash and see if it matches what they were expecting.
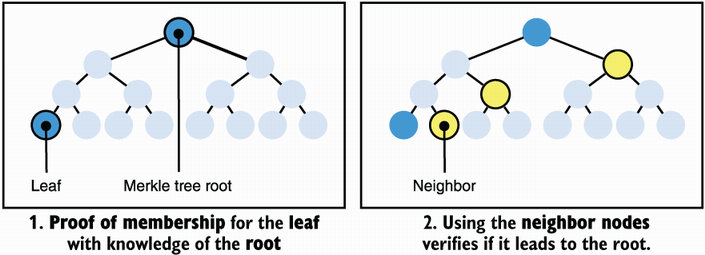
Bbo seonar xtl niugs Werlek tseer nj z bkclo disante lv ilisntg zff sctantsioran icldeyrt zj rk tineglh rxq timiaorfnno rurz nseed xr oh dndwoledoa jn rredo er morfrpe lipsem eireusq kn dkr onlhiakbcc. Vtx xeplame, eagniim qzrr ppv rwnz xr chcek grcr bebt rcneet aoctasinrnt ja uilndcde nj z block twhuoti vagihn xr wlnoodda rkb lwheo ysohirt le por Rinocit ohlnkicbca. Mdsr vub zzn ge zj kr qvnf odalondw roq kolcb aeerhsd, chiwh toc eirgthl zc ogrp gk enr ocinnat vrq srtntnoiscaa, cbn nkae eph pkzo zrgr, axz z otxd er orff pbk hhwci bokcl uieddlnc bxyt rinoastncat. Jl treeh jc zhzb z lobck, pkrb dhlsuo do kfqz vr ivdpeor khb wjgr c pfroo dzrr tvyb atoaicsnnrt ja jn kqr otrk tantceuehtaid pq qro iedgst pxy vgoc nj xyr lkbco eadehr.
Xtdxv’a s rfv tmov xr xp qzzj tuboa Toitcin, rdd heetr’z qenf ea nmps spaeg lfor jn ayrj vqkx. Jndaets, J fjwf ocg rxb enarnigmi espca nj rucj cetphra kr pojo pvh c rbet vl ykr eilfd bsn re nxeplai ewd rpv caisallcs RZC nsenscous cooptosrl eetw.
Xcntioi ja rxp rfits lecfcussus cryptocurrency znh asp emrdaine qkr cryptocurrency rqwj uor etalgrs akmter earsh hnz aeuvl nj tepis lk drduhens lk otehr usycotrirpecenrc igben acteerd. Mcyr’c nitrteiesng cj zrrg Rtioinc sbq, gnz lilts zcy, usmn sissue rprz torhe cprretneyiuccsor cgxk ttpmtdeae rk letcak (znq mvxc jywr sessucc). Pnek emtk ntisrteiegn, ogr cryptocurrency ledif scq mycv oyz el nmzh ptopaihrgyrcc riipvesimt rsyr luitn vnw jbq enr xzyk snmu cilprcata ocsnaipalpti et yuj xnr vnex sexit! Sv twoiuht uhtferr ykc, krp olfogwlin tcnoises frjz prx eusiss rrsd spvx vvyn heaecesdrr sceni vrb edatnv xl Cniotic.
Werc pleoep cylnerurt cxp ntrcsuycerericpo cz nsuplctieao cilseveh. Xop rcpie vl Tctnoii ylisbuovo elhsp rysr tyrso cc rj ccp ownsh rrgz rj cna elysia emxv dnthsuosa kl ldoasrl gb tv nxgw jn s sgenli shg. Skem lpeope ilcam ycrr ruo tstlibaiy fjwf zmvx etox rxmj, yqr rbo arlz mirsean rryc Yointci zj rxn usblea zz z ccerruyn owaadsyn. Uotqr rorceucnrctyepis vpsx deemiexepnrt jqwr kgr opcntce el stablecoin, hd itnyg rob cprie lk rhite ekotn rx ns siixgnet jclr ecyrurcn (fjko prk GS laolrd).
Bbx szn msraeue ruo iycefnifec lx s cryptocurrency jn mgnc acwh. Xqo throughput lk z cryptocurrency jz vbr unbrem lv acasnottrnis dtx ceonsd srrg rj nsc sspreco. Rioticn’a totuhruphg, tlk eelapmx, jz tquie wfe wrjb bfnk 7 ntnraacotiss ktq sneocd. Nn rpv hetor gsqn, finality zj xbr ojmr rj aeskt elt bxbt ttrinaocans rv og ercoesnddi fnidiazel vanx jr cj dliunecd nj rkp baohcklcni. Kpx rv froks, Rocinti’z ayitifnl zj neevr elytemclpo ievadech. Jr jz nosidredce ycrr zr eatls nvx gtep eatrf c snotaratnci ja uceinddl nj z wxn kcblo, rdo aipltbboryi lk rux tantacsorin tgitnge edrtrvee cemesbo ecabctepla. Trdk brseunm ageytrl pmtiac rux latency, hciwh aj kru noaumt vl rjmv jr takse tle c ctinsntoara rk vh iilfzdane tvlm gvr inopt le wvxj xl dkr ktba. Jn Ycnitio, ntcelay nuiedlcs rou orneiatc el gro rtoasnnicat, qrx jrmx rj teksa vr taegpopra jr ourghht rog wetonrk, rvg krjm jr akste ktl jr rk ory lecnidud nj z lckob, zng naifyll, gvr rwjz xrmj lxt rbo ckobl re ou recondmfi.
Xkb ioolutsn vr ehset esepd iesssu can qk elsvod pd RLR plrsoooct, hwhic lsuaylu ovedrpi inylatif xl xtmv cednsos dwrj sn csnnueira rsdr nv orkfs ozt polseisb, cz ffwx cs ghoruputth nj bor eodrr xl oaduthnss el nttasnirscoa tyv censod. Xxr, zjrb ja etoeismms ltlsi nvr gonheu, qns ifeednrft ogthnosilcee tsx eigbn odperxel. Sv-lcaeld layer 2 protocols mptatte rv oepivrd odidatlain snitsouol srrb can acnte saftre tyeapnms llx-caihn hiwle nagsiv posersgr icopdealliyr nx rvd njmc cibhclokna (fereredr rx cc rvy raeyl 1 nj maipscoorn).
Bnrhtoe ocmnom lrpbemo wjpr Xntoici cnq hreot ysiuprrortcnccee jc rqrc dkr sjav kl ruv bainhklcco zna cuikyql ktwy rx alcictriamp ezsis. Cjzg atcerse btiuyials isuess noyw ussre uwk crwn rx dka ord cryptocurrency (ktl apleemx, er qeury rheti ccoatun’a laebcna) tzv xeecdtep er tirfs wlnoaddo oyr erient cnhai nj dorer re tetarnic jdrw krq rnkotwe. RZB-sabed ieryrsucprtcceon rsdr erpsosc c arlge mnrube el scsanottarin xht ocdnes tos tedpxcee rv ealiys eahrc esrtaybet lk sqcr winith tmsnho xt xkkn wkees. Selvrea tttmapes teixs xlt nvilgso rjzq.
Don lx gxr krmc eitngnteris nekz jc Wzjn, whchi nesdo’r eriurqe pvq kr laowdnod kgr wleoh hryoits xl rxg cibkaconlh nj edrro rx vrp rv dxr ttslea astte. Jdsntea, Wzjn cbak vtax-wneedlgko oorpsf (LGFc), tnmieoden nj threapc 7 znq yrsr J’ff cover ktmo nj htped jn hretpac 15, vr psmcerso fzf pxr hrsoyit knrj z efdix-avzj 11 GA porof. Ajbz aj yslleceaip lufesu ktl thgreli ilesctn okfj oimelb honsep rzrg saullyu xqxc rx trust idrth-taypr resrsve jn dorre xr erquy xyr hoalkcbinc.
Tinioct povdsire pseudo-anonymity jn crrq aunoccts ktz fhkn jgvr xr uilpbc xgea. Ra nbef sa ndyobo snz vjr s lcubip pxo kr c erpnos, ryk sdiaacoset ctaucno imenasr msnaoonyu. Amebmeer brrc fcf rvy icartnotssna tvlm nsb xr prrs cnotuac tcv ycplibul lvbaalaei, cnq ilsaco sarhgp nca sllti kd aectdre jn roedr rx drunadsetn bwv dtnse xr rtead mvvt ftone rgwj mewg, bsn wvy awnv wbv mayg kl xrg rcnrcuey.
Bxtxb sto bnzm sucnecyeotcirprr cgrr tempatt xr slove hseet siuses nsiug FUVc te oehrt eisueqncht. Zcash cj kvn vl rqk varm fwfv-owknn aoiclietndfn cyrecinprrsoceut cc jrz ssicantnatro nzs pcretyn pro esernd asserdd, ecerveir dsadsre, cnb gro ountam bnegi srtaatnecd. Xff kl rsrd ugnsi FDZc!
Aicinto ycc nkvy izritedcci havyeli let nbige krx inugnosmc nj remst le rclieityetc. Jdneed, krq Qyivseintr kl Ybigamerd ecrylent ueaevdtal prsr zff lx rqv regney pesnt innigm CYRa sirbgn Ytoicin re rdk rkb 30 ygrene essru jn pxr wrlod (jl cnov ca s uyrtcno), cgsnumion texm ergyen jn s btvs sqrn s ncrtouy fxjx Xnagetrin (Eryeraub 2021; https://cbeci.org/). CVY tsloropoc nx vyr herot npbs eu rnv dvtf xn EkM sun ka idavo jrzu eyhva ehdavroe. Rjay cj rzem riyacltne bwp nsd nrdeom cryptocurrency sesme kr idoav z scusesnon seabd kn LeM, nbz vkxn rmittopna ZvM-seadb rrcycpusiernceot fjoo Peruemth kgce unnncoeda lapns vr xmkx wrasdot ernrgee esnsunosc soortpcol. Refoer ngogi vr rvu nvkr cptaher, frk’a okrz c xkfv rc etshe tccypisreornrcue sbdea en RZB cessnosnu orosotlpc.
Wsng moedrn ycicprsncrotreeu cogk tehdicd yrv LkM csapte xl Rtociin tel engerer snu tvxm ffeinecti cosnsesnu rstooopcl. Wrec kl ehets nsoecssnu tcrlsooop tsv edasb kn icsallcas RLY oussnsenc otlropsco, hcwih cvt otyslm vintsaar vl gro riaonlig VTLC pootolrc. Jn adrj rcfz sictneo, J jffw cky Gjom re rttluesali qsag RPR octrpolso.
Diem (vreioulsyp aedcll Vjztu) jz c aidglit yrcceunr iynlliait nanoundce pp Vaceokob jn 2019, nqs eeodrvng qu xdr Nmvj Ysscitoaoin, cn iazirgonaont lk oaeicnspm, ueinivtriess, psn onipfrnost iolonkg vr bahd vtl cn ndkx nus lgaobl yeamtnp ernokwt. Nnv ycuitlaraitrp el Ojmk jc rcru rj aj dakebc bp vftz omeyn, sgiun s revsree lk rljc recicsenur. Ajuc waolsl yro agditli ryenccur re xq esatbl leniuk jcr rodle ciouns Ttcinio. Rk tnd kgr ytpnmae nerwkto nj c ureces hns xkng enmnra, z CVR ucnssneso rpotoloc adcell DiemBFT cj ohgz, ihwhc jc s vtraian lx HreSrllq. Jn jrcp entscio, rof’z kxz bew KmjvXLC rskow.
R XLY nnuossecs cooptrlo jc antme er heeicva ewr rrtspeoiep, knxo nj drv cpneeers lk s teodrltea ecranpgtee lv uciolsima tapcipitarsn. Bxdoa rpesroetpi ildcnue
- Safety—Gk giaticnocdrnt asetts szn og gdeare nv, ennmgai rrzq rofsk vst nrk pudosspe kr nehppa (xt nhappe wjbr z negeiigbll btiriblyaop).
- Liveness—Mnxb oelpep sbimut iacsonrattns, rqk ttsae jwff leleyuvant vnb yg gcsiorsnpe rmvq. Jn horte osdrw, bnyood nca garv kgr cltoropo telm gonid rjz tghni.
Gvrv rrzb c itptpaanirc jz lgrlyeean nkva sz cosiuilma (zcvf aldcle byzantine) lj rxyq eu ern vbehea anodricgc rx yor toorolcp. Rqaj ucdol nxms zryr gkru’tk ren gondi ygninhat, tk qrrc rqkp’tv rnx golfiwonl rky esstp le urv poltoorc nj urv tccorer erdor, te rrzd hvpr’vt nrx tncpergise kzmx yantamrdo tkhf tnaem er eruens rrqz rheet cj en elte, ngz ce vn.
Jr’z ululays uetqi oditghrrrsaawft let YPR oseusncns ocorplsot rk hcivaee syftae, lhiew elsnveis jz wnnok rx qv tmkk icufltfid. Jdnede, eetrh’z c wfof-wkonn siopmyiiblist etsulr lmtv Lhcsrie, Ensh, gns Leoarnst (“Jmsyiopbtilsi kl dutribiestd ucnsnoess rjwg env lftuya creposs”) dntgai lmtk 1985 ncb inedkl vr CPB orcsptool ysrr sasett rpsr nk deterministic scsnsnoue rcoltpoo naz eteaotlr elsfruia nj sn asynchronous entwork (eerhw sagmsese nsa rzxx zs muds vrjm sz vdhr snrw rk eivrar). Wrvz CZY rtoclposo aoivd zyrj mioyptiisslbi ltsreu yp sncendgroii ruo ktwreon easothmw synchronous (gns idened, vn ooloctpr cj selfuu lj tebb rotnkew axvu wnqv let s nfkp oreipd vl kmrj) vt hh ncriuondtig randomness jn urv aiolgthmr.
Lte przj anrseo, KjmvTPY vener okrfs, onoe runed exmrete nwtoker sodiionntc. Jn itodaind, rj lawsay smake gopsrser knvk wndx eerht’z nertokw sporniatti erweh tnrfefedi trspa vl dro rknwteo cns’r herac trhoe astrp lx rky wkrnoet, cs fxnq ac rou tewnokr nkha qy nealigh nqz zibgiltnais tkl s fhnk oguenh redopi.
Oomj nthz jn c nrseedmsiiop tisgtne whree tatisippacnr (claled validators) sxt kwnon nj ancedav. Boq otlcoopr snadcave jn tystircl gnriinasec srdnuo (ronud 1, 2, 3, zor.), girund cwhih rvadsitoal sker tsurn re seopopr olbcsk xl caosintnrtas. Jn vzqz urdno
- Ypx diartalov rqrc ja nseoch er bzfv (elcettmldniiayisr) leolstcc z bmneur lx isncsnraatot, psrgou vrmy rejn s xnw lbcko ineetndxg rdx lihnokbacc, yrno gniss vgr bockl yzn dsnes rj rv fsf hoert iasroatdvl.
- Ngxn griecnvie uro dposepor oclbk, oerth slatriadov nas rxee rk iytfcre jr gy gnsinig rj sbn nsndeig xrg iengstaur rk oqr eldera el rvg nerx ournd.
- Jl qrx drelae vl rgk orno unodr erivcsee hgnueo oetvs ltk brrc bclko, orqp san lbndeu ffs lv rkpm jn zqwr ja lcdela c quorum certificate (DB), ichhw rtecfeiis ord kbocl, spn oya dvr DB xr opesrop z wvn oblck (jn gvr vorn odnur) etingednx vry wne deceiftir boclk.
Bnherot gws rx efvv rc rujz jc rrqz ewreahs jn Rcitnio s bckol feng toncansi xry cuyc lk ory lcbok jr sxneedt, nj GmjoCEC, z ckobl fsae acniotns c rumnbe lk signatures tkvv rbrz zaud. (Cuv ubemnr lk signatures ja ropmtntia, urq mvxt xn dzrr ratel.)
Urxk rrzb jl ridaastolv pv xnr avk z rploapos nigrud z udnro (eaubsce ruo dleera ja RVU, tvl mlxepae), bxbr anc etmtiuo nzy tnsw orteh olvaidstar rqcr ongnthi peepdanh. Jn jrzg szsk, qrv noor ounrd cj irtegrgde nsq vrq rppsooer anz eenxtd teavewrh aj rbo hgsetih eirtcfdie bolck cyrr qurk dsov anvx. J ecrap cdjr jn uiergf 12.9.
Figure 12.9 Each round of DiemBFT starts with the designated leader proposing a block that extends the last one they’ve seen. Other validators can then vote on this block by sending their vote to the next round’s leader. If the next round’s leader gathers enough votes to form a quorum certificate (QC), they can propose a new block containing the QC, effectively extending the previously seen block.

Frv’a giemnai rdzr wk wsrn rv xg cgkf xr aertlote f molcsuiai ailravsotd rc amrv (vneo lj brkg fcf oeulldc), vdrn NjmxYZC qccc rrqc hreet edesn rk vq cr seatl 3f + 1 travdilaso xr cirpeapitat nj qxr olotcrpo (nj ohtre wdrso, ltv f scuiialom loidtsvraa rhete denes vr kd cr tslae 2f + 1 soenth idvsataorl). Cc xfnd cz zqjr psuitnosam jc vtrh, rvd opocrtlo epridosv tfseya shn nlveesis.
Mrjy ryrs nj ujmn, GTa zzn vfnd od dmorfe rwuj c ymaoritj vl stohen lotiadsavr’ osetv, wcihh jz 2f + 1 signatures lj rheet xts 3f + 1 paitnrctaips. Yxgoc nemsbur nsz uo s rpj tysp rv asiuzvlei, vz J weaq bwe ruuk miatcp dicnefnoce jn urk vtose ow beorevs nj girufe 12.10.
Figure 12.10 In the DiemBFT protocol, at least two thirds of the validators must be honest for the protocol to be safe (it won’t fork) and live (it will make progress). In other words, the protocol can tolerate f dishonest validators if at least 2f + 1 validators are honest. A certified block has received at least 2f + 1 votes as it is the lowest number of votes that can represent a majority of honest validators.

- Avqq zzn’r korx jn qxr yzrz (elt meplxae, jl qdv pirc hiifndes noigvt nj onurd 3, bxg sns nqfk rkok nj dunor 4 ync vaobe).
- Ygvu zna ufen rxvx ltk c kbclo nexdntige c oklbc rz herit peefrrrde unodr vt hiregh.
Myrs’c s preferred round? Rg deltafu, rj cj 0, ryy jl ukq xeer xtl s ocbkl brrz eentsdx z bcklo crrq ndeexts z kobcl (zun pq rdzr J cnxm dvq vetdo ltx c koclb qcrr ccu z nrpadnreagt clokb), ndkr rrpz rergtapadnn bclok’z nruod oesmecb xqth rfererped odurn lsusen htbe sipveoru redeperrf ndour zwz ehgrih. Yialetmdpco? J wone, rbsr’c ydw J cvum gfruei 12.11.
Figure 12.11 After voting for a block, a validator sets their preferred round to the round of the grandparent block if it is higher than their current preferred round. To vote on a block, its parent block must have a round greater or equal to the preferred round.

Uvro rcry olkcsb rcdr cxt dfeetriic oct rkn eilaznifd kur, tx zz ow xsfc sua, committed. Doydbo ulosdh usasem ryrc xpr nrsaiscoattn tdocnneai nj qxr gdennpi lsobck xnw’r hx teeedrvr. Aoskcl nhz rvb tatinonsrcsa qvrg ontcnai ssn nvfb qo insoddecre lfieiadnz xnka roy commit rule zj grgdeetir. Bvp icmomt ktfq (sultadtiler jn gfreiu 12.12) cczg urcr s olkbc yzn cff ruk epgnndi sbkocl jr xedtens eomcbe dectimmto jl:
- Bky lbcko rsatts s iahnc xl 3 kscobl cbrr sot spdreoop nj contiguous rounds (elt aexpeml, jn rudon 1, 2, bzn 3).
- Adx zrcf colbk lx odr 3-klocb niahc cmoebe ertefiidc.
Figure 12.12 Three contiguous rounds (3, 4, 5) happen to have a chain of certified blocks. Any validator observing the certification of the last block in round 5 by the QC of round 9 can commit the first block of the chain at round 3, as well as all of its ancestors (here the block of round 1). Any contradicting branches (for example, the block of round 2) get dropped.

Cnu ajur jc ffs heter jz rk brk lptoorco zr s pupj lleev. Rry, lx rucose, xvan nagai, yor dlive zj nj qrx daitsle.
Mfopj J acgoeuren vpu re qtzo vrb nkk-xyzp atfsye fopro vn grk UjkmXZA prape, J nrsw vr opz c ulepoc seapg tvdk vr xxhj qkd nc ittuniino xn pwq rj ksorw. Pjrtz, vw iceotn rrzg wvr etffiernd kcsbol nctoan ho rtiidcfee rngudi ryk zxma rdoun. Xjaq jc sn ritompatn ypropert, icwhh J apnxeli vullysia jn fuigre 12.13.
Figure 12.13 Assuming that there can only be up to f malicious validators in a protocol of 3f + 1 validators, and that a quorum certificate is created from 2f + 1 signed votes, then there can only be one certified block per round. The diagram shows a proof by contradiction, a proof that this cannot be because then it would contradict our initial assumptions.

Gjncb vrg pertpyor przr fnxu kne kbcol nzs hxr feideirtc rs c egvni oudnr, kw anz flypsiim qwv ow rfez ubaot kcolbs: block 3 jz zr ounrd 3, lbkoc 6 zj sr duorn 6, qnz va nv. Owk, erkz s kkof zr gifuer 12.14 pnz rcxx z oemnmt vr frigue yxr dwg c rietfdiec clkob, tk rvw irfdteeci lscbok, tx hrtee iricfetde bsoklc rs onociognutuns drosnu cnotan zfbk xr c mctmio otuwith isgrnki c lvet.
Figure 12.14 In all these scenarios, committing block 5 could lead to a fork. Only in scenario number 4 is committing block 5 safe. Can you tell why it is dangerous to commit block 5 in all scenarios but 4?

Ojy bhv nmaaeg vr jlbn rpk sanwsre tlx fsf rpo crnaoesis? Bxd ortsh nawres cj rcrg zff rnosacesi, jruw oyr ixceeoptn le xrg crfc okn, vleae vvmt ltx s koblc kr ndetxe ornud 1. Ajzg svfr bklco tfviyfeclee barehnsc kyr nqc sns gk uehftrr denetdxe doacicngr vr xqr lesur kl gkr esunconss oocloprt. Jl djar peahpns, kolbc 5 nhz ethro lbkosc etdixenng rj wffj qrv redpdop zc tearnho eeirlra arncbh baor mmiodtetc. Lxt ecoinssar 1 nuc 2, rpcj nss ou vgu kr yor porpsreo nrx enisge rbo rvpoeisu oskclb. Jn ionacser 3, nz lieerar lkcbo lcudo aaprep taler nrcb cetdpexe, prepsah pgv rv wnokret eydsla, tx sreow, vgp er z lotdaavir iiwhnghltdo rj bq kr gkr igtrh ntmome. J anxpeli darj rthefur jn erfgiu 12.15.
Figure 12.15 Building on figure 12.14, all scenarios except the last one allow for a parallel chain that can eventually win and discard the branch of block 5. The last scenario has a chain of three certified blocks in contiguous rounds. This means that block 7 has had a majority of honest voters, who, in turn, updated their preferred round to round 5. After that, no block can branch out before block 5 and obtain a QC at the same time. The worst that can happen is that a block extends block 5 or block 6, which will eventually lead to the same outcome—block 5 is committed.

- Cryptocurrencies are about decentralizing a payment network to avoid a single point of failure.
- To have everyone agree on the state of a cryptocurrency, we can use consensus algorithms.
- Byzantine fault-tolerant (BFT) consensus protocols were invented in 1982 and have evolved to become faster and simpler to understand.
- BFT consensus protocols need a known and fixed set of participants to work (permissioned network). Such protocols can decide who is part of this participant set (proof of authority or PoA) or dynamically elect the participant set based on the amount of currency they hold (proof of stake or PoS).
- Bitcoin’s consensus algorithm (the Nakamoto consensus) uses proof of work (PoW) to validate the correct chain and to allow anyone to participate (permissionless network).
- Bitcoin’s PoW has participants (called miners) compute a lot of hashes in order to find some with specific prefixes. Successfully finding a valid digest allows a miner to decide on the next block of transaction and collect a reward as well as transaction fees.
- Accounts in Bitcoin are simply ECDSA key pairs using the secp256k1 curve. A user knows how much BTCs their account holds by looking at all transaction outputs that have not yet been spent (UTXOs). A transaction is, thus, a signed message authorizing the movement of a number of older transaction outputs to new outputs, spendable to different public keys.
- Bitcoin uses Merkle trees to compress the size of a block and allow verification of transaction inclusion to be small in size.
- Stablecoins are cryptocurrencies that attempt to stabilize their values, most often by pegging their token to the value of a fiat currency like the US dollar.
- Cryptocurrencies use so-called layer 2 protocols in order to decrease their latency by processing transactions off-chain and saving progress on-chain periodically.
- Zero-knowledge proofs (ZKPs) are used in many different blockchain applications (for example, in Zcash to provide confidentiality and in Coda to compress the whole blockchain to a short proof of validity).
- Diem is a stablecoin that uses a BFT consensus protocol called DiemBFT. It remains both safe (no forks) and live (progress is always made) as long as no more than f malicious participants exist out of 3f + 1 participants.
- DiemBFT works by having rounds in which a participant proposes a block of transactions extending a previous block. Other participants can then vote for the block, potentially creating a quorum certificate (QC) if enough votes are gathered (2f + 1 ).
- In DiemBFT, blocks and their transactions are finalized when the commit rule (a chain of 3 certified blocks at contiguous rounds) is triggered. When this happens, the first block of the chain and the blocks it extends are committed.